In this post I will detail how to configure F5 Access Policy Manager (APM) with Microsoft Azure Multi Factor Authentication (MFA). In this scenario APM is deployed as a Single Sign on Portal (SSO), however the logic remains the same if you were using APM as a front end to any internally hostewd application. In this example F5 APM is configured with radius for the MFA functionality. That is APM will talk Radius protocol to the Radius server once a user has passed Active Directory authentication.
Prerequisites
1. Make sure your Radius server setup and configured with Microsoft NPS extensions for Azure. The Azure tenancy should be configured to accept Radius requests from your NPS server.
2. Radius clients should be configured for the F5 self ip addresses
3. Users from your internal AD should be synched to your tenancy and enrolled in MFA. All of this is out of scope of this post.
F5 APM Configuration
1. Configure the Radius server from Access > Authentication > Radius. Set the server addresses and the secret key (they must match what is configured in the server). Set the timeout to 60 seconds. Click Update.
2. Now you need to either create an access policy or edit an existing one. Access > Policies / Profiles > Access Profiles (Create or Edit). I have one existing so I click the edit link to bring up the Visual Policy Editor.
3. Edit your Logon Page and make sure Split domain from full Username is set to yes. We only want to send the username value to the Radius server for MFA.

4. You need a new step after the AD Auth step to assign a new variable (+ variable assign). Call it as follows: session.logon.custom.pass = mcget -secure {session.logon.last.password}

This configures a fresh variable for the users password which can be assigned at the SSO Credential Mapping step. It allows users to use the push notification and the passcode methods of Azure MFA.
5. Add another step after the Variable Assign. Select + and Radius Auth. Call it Azure MFA. Select the AAA Server as the Radius server you created in step 1. Click Save.
6. Now edit the SSO Credential Mapping step and change SSO Token Password to Custom: mcget -secure {session.logon.last.password}.

This maps the variable from post authentication but before Azure MFA step. If the APM SSO module is not configured in this way the users password variable would be changed to the 6 digit passcode if the users authenticated using that Azure MFA method.
7. If you created a new policy go over to Local Traffic > Virtual Server. Click on your VS and scroll down the Access Profile and set it to this new MFA one. This allows you to retro fit MFA to Virtual Servers with APM.

I have succssfully tested this configuration using Azure MFA methods:
– Push Notification
– Passcode / SMS
– Phone Call
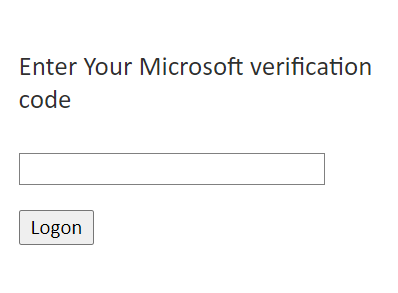
The F5 will show a second page for the Code input if the user has this method as the default.

As a side note the easiest way for a user to update the default Azure MFA method is to use the My Sign-ins tool.
Comments